Cisco Prime Infrastructure Cisco Prime Infrastructure (CPI) is a converged solution that combines the following wireless functionalities: Cisco Prime Network Control System (NCS) Cisco Prime LAN Management Solution (LMS) CPI is useful in accomplishing the following tasks: deploying end-to-end network infrastructure maintaining end-to-end network infrastructure managing end-to-end network infrastructure Cisco Prime Licences Assurance add-on license - Provides … Continue reading Cisco Wireless: Cisco Prime Infrastructure 2.0 Summary Notes
Category: Wireless
Cisco Wireless: WebAuth on WLC
Web Authentication WebAuth is an authentication method without encryption. It provides Layer 3 security. WebAuth with Local WLC The client (end user) opens a web browser and enters a URL. Client resolves URL using DNS Client sends HTTP request to IP address of the site The WLC URL sends the user to a login page. If authentication is … Continue reading Cisco Wireless: WebAuth on WLC
Capturing WLAN Packets using WireShark
If you are studying for CCNP Wireless or CWNP Certification, an essential part of the study process is actually getting to lab it all out so as to understand the concepts. I noticed that my Wireshark output lacked the 802.11 management or control packets while trying to capture Open System Authentication process. This blog will explain … Continue reading Capturing WLAN Packets using WireShark
CWNA Summary Notes: Legacy 802.11 Security | MAC Filters
MAC Filtering MAC Filtering referes to the use of MAC addresses to client devices that can authenticate to a WLAN. MAC Filtering is not defined by 802.11 Standard and any implementation of it is Vendor specific. Here is an example from my ASUS home router. Weakness: MAC addresses can easily be spoofed. Where used: Protect … Continue reading CWNA Summary Notes: Legacy 802.11 Security | MAC Filters
CWNA Summary Notes: Legacy 802.11 Security | Static WEP Encryption
Static WEP Encryption This is a layer 2 encryption method using RC4 streaming cipher. Main goals of WEP Encryption were: Confidentiality (Data privacy through encryption) Access Control ( Authorization if static WEP keys match) Data Integrity ( Data Integrity Check-sum is computed before encryption to ensure that the data has not been tampered with) Can … Continue reading CWNA Summary Notes: Legacy 802.11 Security | Static WEP Encryption
CWNA Summary Notes: Legacy 802.11 Security | Legacy Authentication
Legacy Authentication Legacy authentication methods were more of an authentication of capability (verification between two devices that they were valid 802.11 devices) and not so much an authentication of user identity. They are of two types: Open System Authentication It provides authentication without performing any form of user verification Involved a 2 way exchange between … Continue reading CWNA Summary Notes: Legacy 802.11 Security | Legacy Authentication
CWNA Summary Notes: 802.11 Network Security Architecture
Components of a Secure Network Required components when securing a network are: Data Privacy and Integrity Access to Wireless medium is unrestricted hence the use of cipher encryption technologies is needed for proper data privacy. A cipher is an algorithm that is used to perform encryption: RC4 algorithm ( Ron's Code / Rivest Cipher) It encrypts … Continue reading CWNA Summary Notes: 802.11 Network Security Architecture
CCIE version 3.0 Wireless Summary Notes 1 : IEEE 802.11 Primary MAC Layer Functions Part 2
Connectivity To connect, the client must go through the following: Scanning for networks Includes passive or active scanning mode (or both). Many vendors use both. Passive scanning: Client tunes to each channel, listens for a period of time, and monitors 802.11 beacon frames (AP transmits beacons by default every 100 milliseconds on a specific RF) Client records the RSS … Continue reading CCIE version 3.0 Wireless Summary Notes 1 : IEEE 802.11 Primary MAC Layer Functions Part 2
CCNP Wireless 642-747 IUWMS Summary Notes 6 : Location Tracking Techniques – Pattern Recognition
This technique is based on sampling and recording radio signal behaviour patterns in specific areas. Commercial solutions usually base the signature on RSSI but it can also use ToA, AoA and TDoA based RF signatures. Deployment of these systems is based on 2 phases: Calibration phase A walk around is done with a mobile device … Continue reading CCNP Wireless 642-747 IUWMS Summary Notes 6 : Location Tracking Techniques – Pattern Recognition
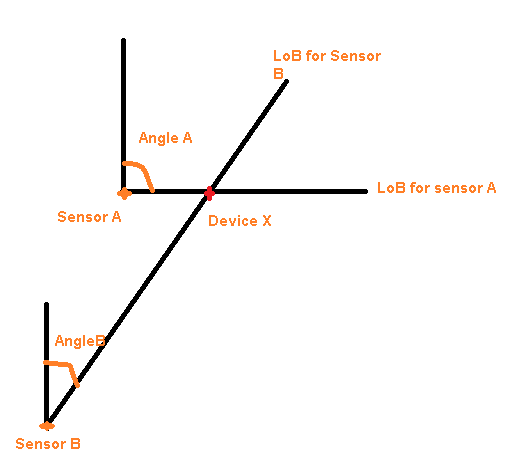
CCNP Wireless 642-747 IUWMS Summary Notes 5 : Location Tracking Techniques – Angulation (AoA / DoA)
Angulation (Angle-Based) Techniques Localization is based on the angle of the received signal. Angle of Arrival (AoA) / Direction of Arrival (DoA) AoA determines the angle of Incidence at which signals arrive at the receiving sensor. This angle is used to estimate the location of the device using the intersection of the two lines of … Continue reading CCNP Wireless 642-747 IUWMS Summary Notes 5 : Location Tracking Techniques – Angulation (AoA / DoA)