Static WEP Encryption
This is a layer 2 encryption method using RC4 streaming cipher.
Main goals of WEP Encryption were:
- Confidentiality (Data privacy through encryption)
- Access Control ( Authorization if static WEP keys match)
- Data Integrity ( Data Integrity Check-sum is computed before encryption to ensure that the data has not been tampered with)
Can be entered as a hex (0 – 9) or ASCII (A – F) characters.
Static WEP Encryption was on 2 forms:
64- bit WEP
This was the original form. It consisted of:
- 40 bit secret static Key
- 24 bit initialization Vector (IV) appended in the beginning of the frame
- selected by radio device drivers
- Is sent in clear-text
- Is different for each frame but there is a limited number of IV combinations (16 million)
Has 10 hex (5 ASCII) characters.
128- bit WEP
It consisted of:
- 104 bit secret static Key
- 24 bit initialization Vector (IV) appended in the beginning of the frame
Has 26 hex (13 ASCII) characters.
WEP features
Many Vendors support up to 4 static WEP keys and the user can choose one as the default key transmission.
- The transmission key is the static key that is used to encrypt data by the transmitting radio.
- Client may use one key to transmit outbound and a different key to decrypt received traffic
- For encryption / decryption to work properly, each of the 4 keys should match on with ends.
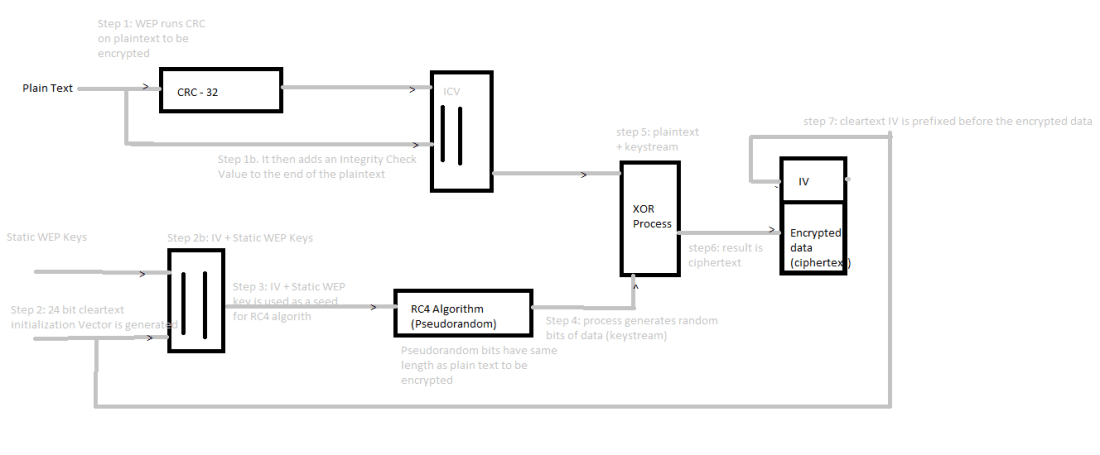
How WEP Encryption works
WEP Attacks
- IV Collision attack – The IV is sent in clear-text. The attackers can eventually recover the secret key given that the IV will eventually repeat itself in busy networks.
- Weak Key Attack – Attacker can recover the secret key much easier by recovering the known weak IV keys which are generated because of RC4 – Key scheduling algorithm
- Re-injection Attack – Packet re-injection attack launched using hacker tools can be used to speed up the collection of Weak IVs on the network with little traffic.
- Big-Flipping Attack – The Integrity Check Value data integrity checks is considered weak, hence WEP encrypted packets can be tampered with.
Disadvantages of WEP
- A combination of attacks 1 – 3 can crack the WEP key in less than 5 minutes
- Use of static keys is an administrative nightmare
- static keys can be compromised via social engineering.
References:
- CWNA-106 Certified Wireless Network Administrator Study Guide by David D. Coleman and David A. Westcott.