For the 2nd challenge we are required to bypass the login mechanism used on this webpage https://02.adventofctf.com. This is the page we get when we navigate to the URL.

I tried logging in with a random username:password test:test. Since we are logged in as guests, we do not see the flag.
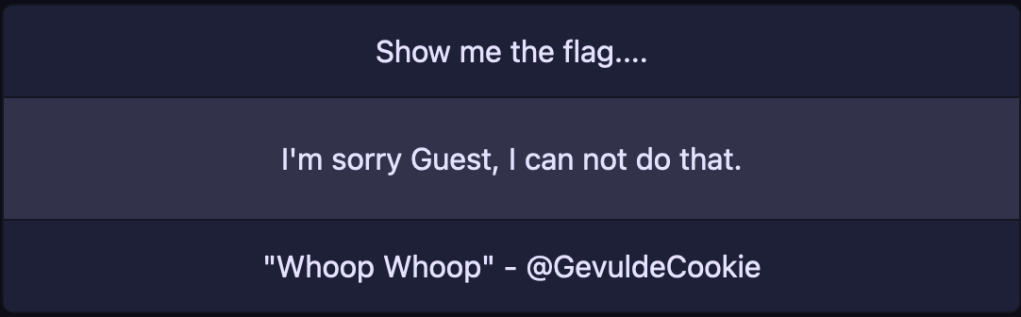
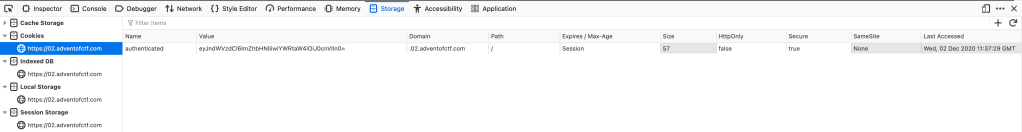
Using developer tools, noted that there were cookies being stored on the page which looks like a Base64 string.
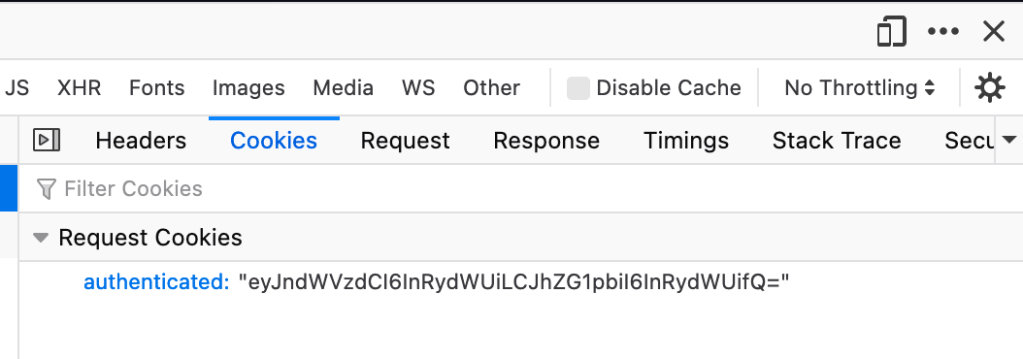
Decoding the Base64 string gives us the value {“guest”:”true”,”admin”:”false”}. Well, I do not want to be logged in as a guest and would like to have admin privileges too.
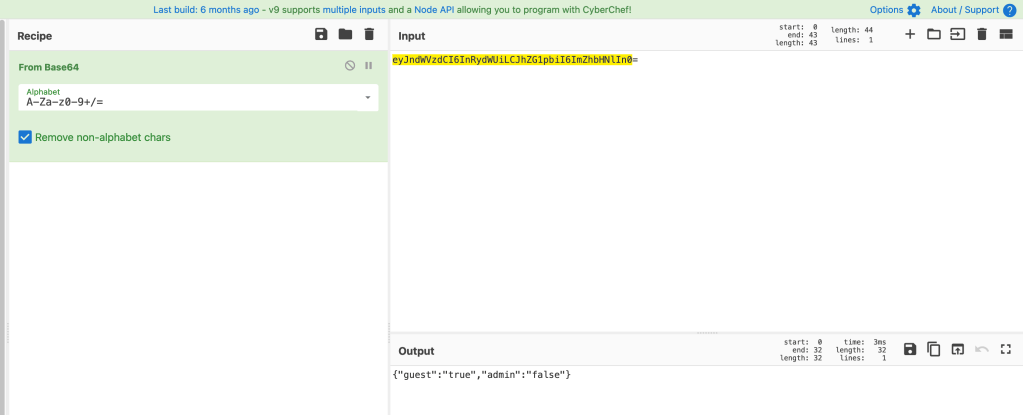
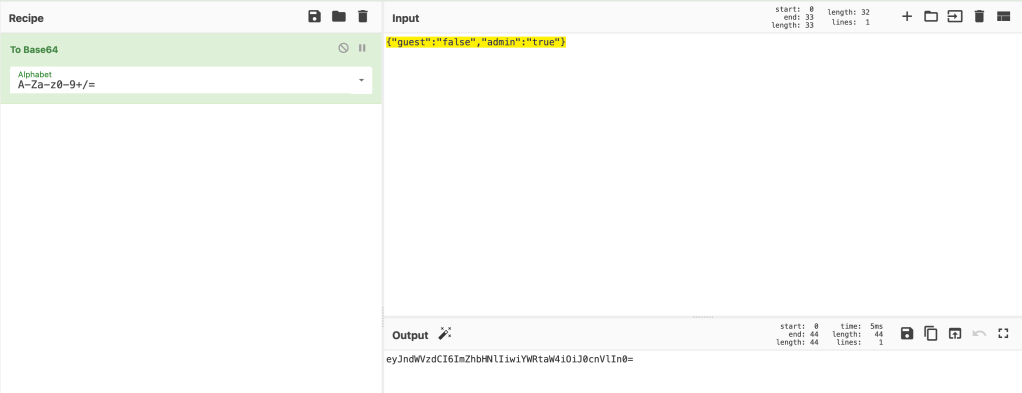
Let’s try modify that cookie value to {“guest”:”false”,”admin”:”true”}. We need to encode it back to Base64. We get a new value of eyJndWVzdCI6ImZhbHNlIiwiYWRtaW4iOiJ0cnVlIn0= that we can modify our cookie to.
We can easily modify that cookie value from browser developer tools, under Storage. Simply double-click on the value field and paste.
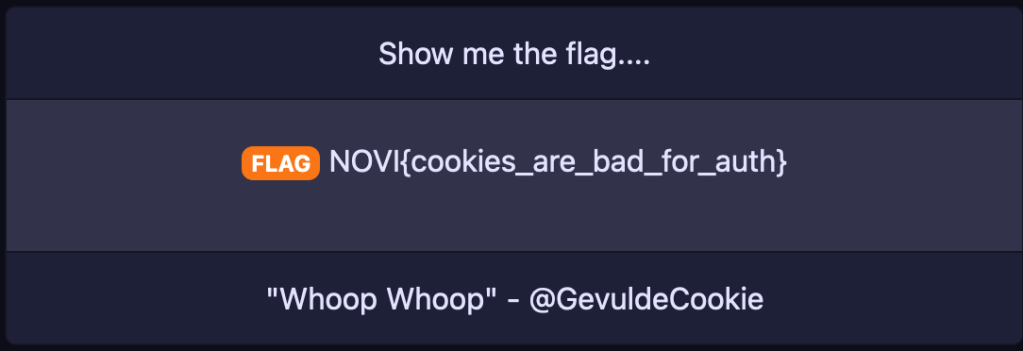
We then refresh the page and get the flag NOVI{cookies_are_bad_for_auth}.
Let’s update the Badge Server