This challenge requires that we bypass the login mechanism used on https://03.adventofctf.com.
Let’s see what Developer tools has to offer. I tried filling in the form with username test password test but I see no activity in Network tab which is odd for HTTP(s) traffic.
I went ahead and inspected the source and found a script reference to Javascript. Looks like when we submit our credentials the form calls a function checkPass()
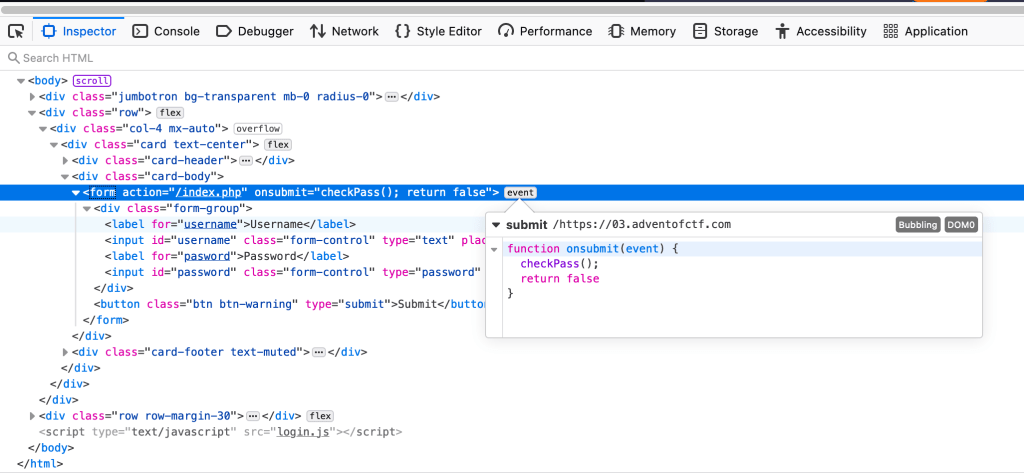
I suspect that function is referenced by the script we see at the bottom whose source is login.js. Let’s try navigate to that path https://03.adventofctf.com/login.js. Sure enough, we see the function.
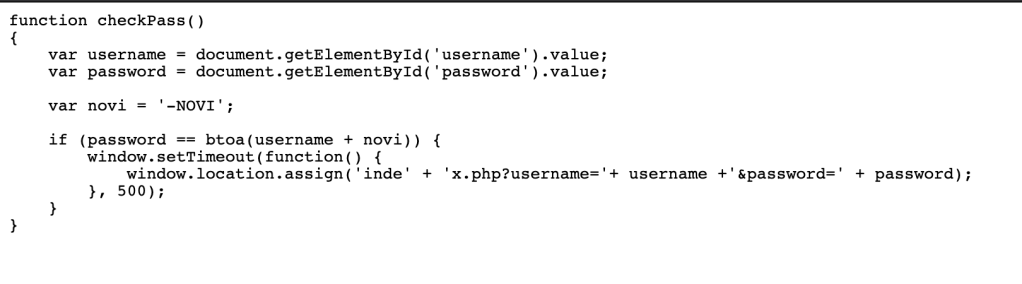
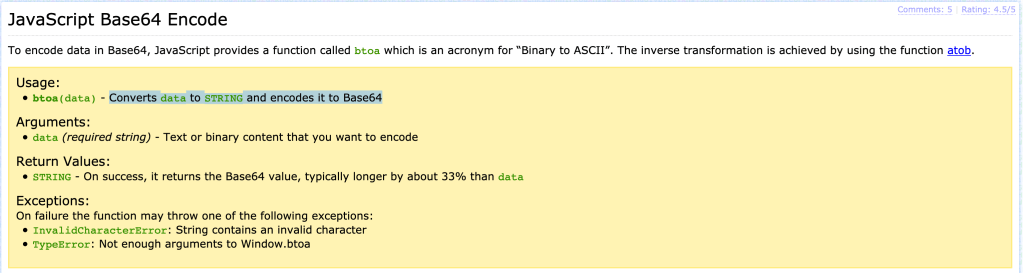
Note the part that verifies the password. There is a function btoa() that is triggered after combining the username with novi. That value is compared to the password. But what the hell is btoa()?
if (password == btoa(username + novi)) {
window.setTimeout(function() {
window.location.assign('inde' + 'x.php?username='+ username +'&password=' + password);
}, 500);
Let’s ask our friend Google what btoa() means. Several resources like this one here at Base64 Guru point to it being a means to convert data to string and encode it to Base64
Since this btoa() value is being compared to our password, lets try figure out the value of btoa(username + novi). Returning to the variables just above the if comparison, we see that the username value is simply taken from the user input “username” field and the novi variable is -NOVI.
var username = document.getElementById('username').value;
var password = document.getElementById('password').value;
var novi = '-NOVI';
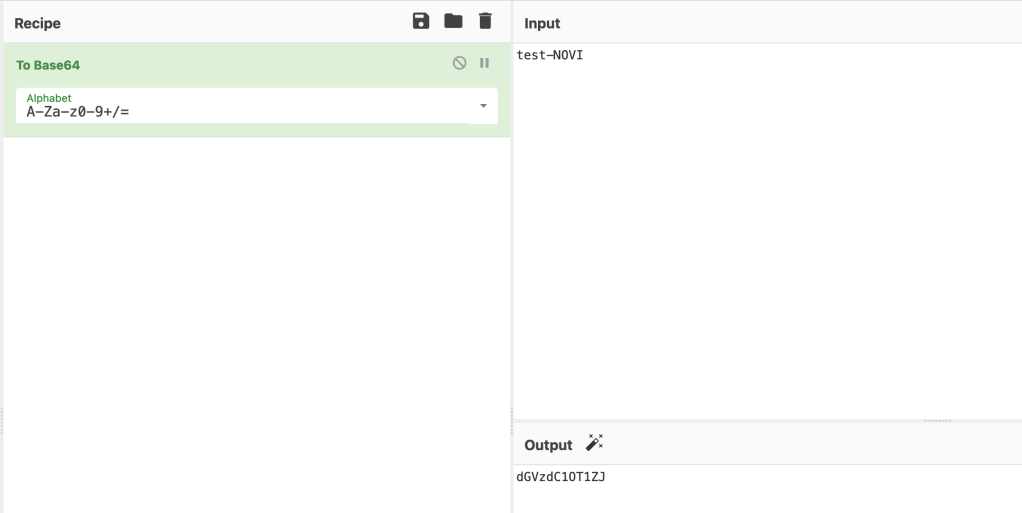
In my case, username=test so the string username+novi is test-NOVI. Converting that to base64 in CyberChef gives us dGVzdC1OT1ZJ.
Now that we know what the password should be dGVzdC1OT1ZJ, let’s use that as a password for username:test and walaah! We found our flag: NOVI{javascript_is_not_s@fe}. Not bad for 300 points :)!
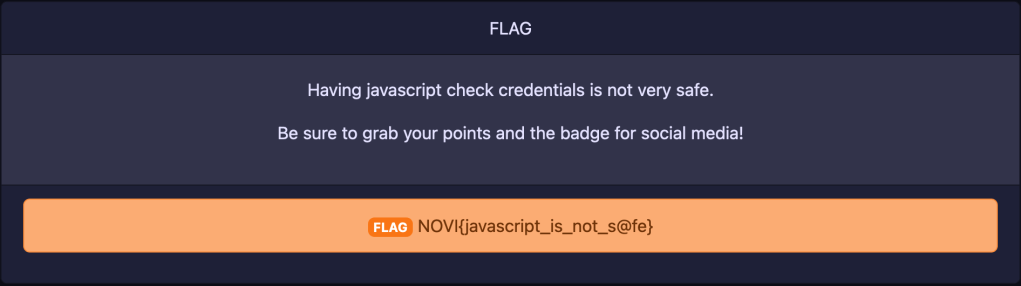
Don’t forget to update the Badge server too.