For this challenge, we are required to bypass a login form using a powerful ‘hacker tool’. Could the reference to hacker tool simply be a distraction?
Again a login form stands in your way. What powerful ‘hacker’ tool will help you proceed?
As usual, we begin by inspecting the source code via Developer tools to see if anything interesting strikes my interest. Nothing!
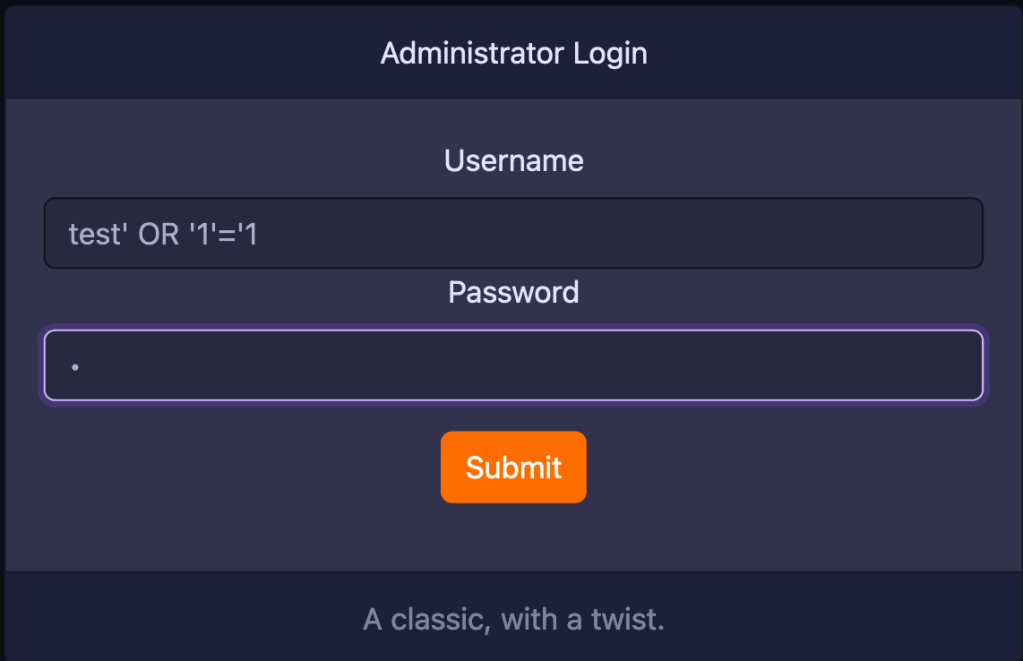
Another usual way to bypass forms would be to try SQL Injection. Let’s just try a using a usual OR '1'='1 in both username and password fields. The aim is to simply see if we get an error from the database.
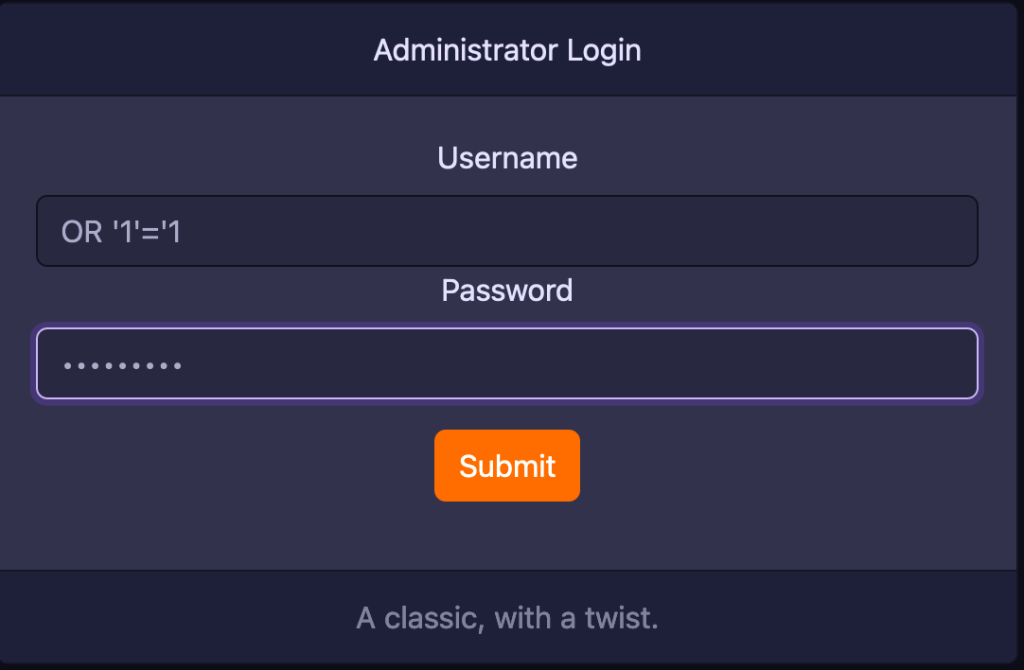
Sure enough, I get the error below from the MariaDB server. This means that we are able to communicate with the Database server.
Error description: You have an error in your SQL syntax; check the manual that corresponds to your MariaDB server version for the right syntax to use near ‘1’=’1′ AND password=’OR ‘1’=’1” at line 1
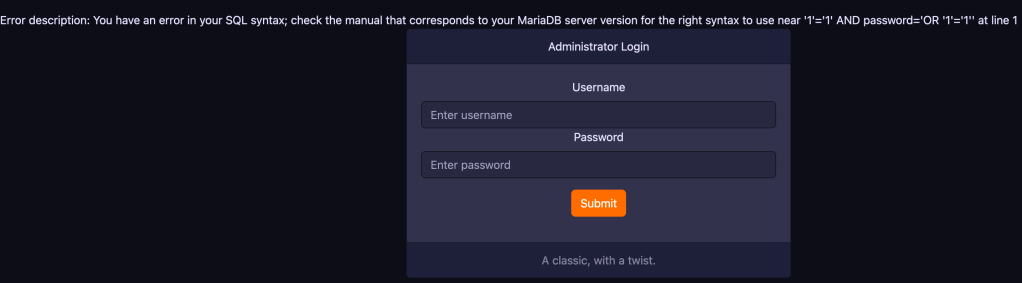
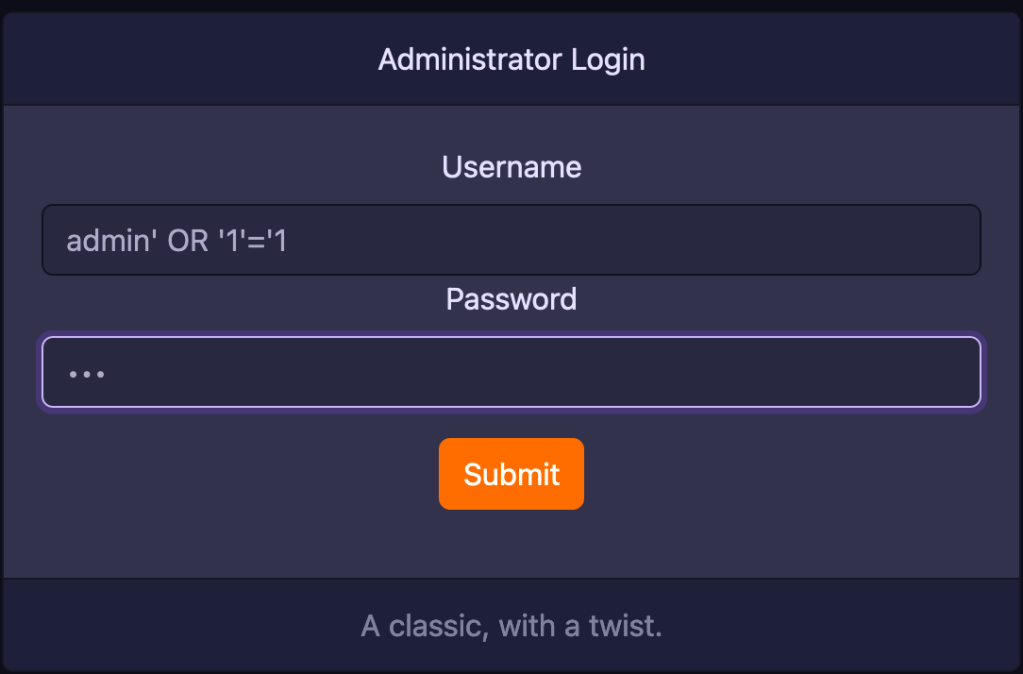
Now, we just have to play around with the SQL inputs to get access. Since this is a login form, we can try a login name and add the SQL payload admin test' OR '1'='1. What we are doing is that we are adding a username and then escaping it so that the expression 1=1 always evaluates to true. Weird, I don’t get anything now.
Replaced test with a bunch of other possible usernames including administrator, root but that did not return anything. Since the page is for administrators, I finally thought to try admin as the login. It really does not matter what password you give.
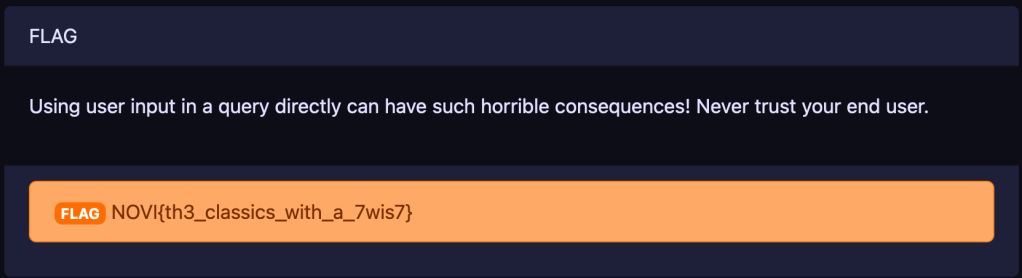
With that, I was able to successfully login and got the FLAG: NOVI{th3_classics_with_a_7wis7}
Don’t forget to update the Badge server too.