Wireless Privacy and Integrity Methods
- WEP
- deprecated
- Temporal Key Integrity Protocol (TKIP)
- Developed by 802.11i working group and the Wi-Fi Alliance
- Adds following features to legacy hardware with WEP
- MIC — Algorithm that adds a hash value to each frame as a message integrity
check to prevent tamperin - Time stamp —Added into the MIC to prevent replay attacks
- Sender’s MAC address — Added to the MIC
- TKIP sequence counter —Provides a record of frames sent by a unique MAC
address - Key mixing algorithm —Computes a unique 128-bit WEP key for each frame.
- Longer Initialization Vector (IV) —The IV size is 48 bits, making it impossible to exhaust all WEP keys by brute force calculation.
- MIC — Algorithm that adds a hash value to each frame as a message integrity
- Should be avoided
- deprecated in the 802.11-2012 standard
- Counter/CBC-MAC Protocol (CCMP)
- Best method so far
- Cannot be used in legacy devices that support only WEP or TKIP.
- Has 2 algorithms:
- AES counter mode encryption – used in US gov etc. Its open and publicly available and most secure.
- Cipher Block Chaining Message Authentication Code (CBC-MAC) for integrity checks
- The wireless network must support both AES counter mode and CBC-MAC in hardware
WPA and WPA2
IEEE 802.11i standard defines best practice wireless security methods.
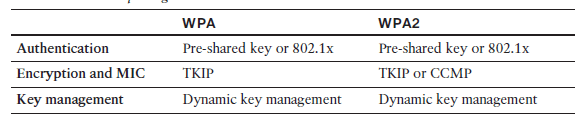
The Wi-Fi Alliance introduced its Wi-Fi Protected Access (WPA) industry standard while IEEE 802.11i standard was being developed. WPA was based on parts of 802.11i and included 802.1x authentication, TKIP, and a method for dynamic encryption key management. They later developed WPA2 standared that is compared below.
Wi-Fi Alliance certifies interoperability with methods like EAP-TLS, PEAP, EAP-TTLS, and EAP-SIM.
Both can have the following authentication modes:
- Personal mode – uses preshared key for smaller deployments.
- Enterprise mode – uses 802.1x EAP-based authentication
Best Practice is to use WPA2 and CCMP.
Management Frame Protection (MFP)
Developed by Cisco to mitigate attacks that leverage AP management frames in 2 forms:
- Infrastructure MFP – APs add a MIC toward the end of each frame. Neighbouring APs in the same infrastructure can understand and determine if the frame has been altered and alert controller. Participating APs compute and tag management frames with a MIC value and then listen
to detect any evidence of tampering. Clients do not participate in this. - Client MFP – only associated clients and neighboring APs can understand the MIC and encryption of the management frames. Client MFP, in contrast, uses a MIC to protect management frame integrity and adds
end-to-end encryption to protect the privacy of management frame contents. Clients must be capable of participating too, to decrypt the management frames and validate the MIC value.
Clients must support CCXv5 and must use WPA2 with TKIP or CCMP.